Apply for a PostDoc/PhD position in my
research group at CISPA in Dortmund, Germany.
https://www.christian-rossow.de
If you can't explain it simply, you don't understand it well enough.
Report - Paper 'Large-Scale Analysis of Malware Downloaders' accepted at DIMVA 2012
In this paper, Christian J Dietrich, Herbert Bos and me explored
malware downloaders that we found in Sandnet. We motivated our
research by the fact that such downloaders are responible for a
huge number of malware installations. We were surprised to see such
a diversity in the downloader landscape, not only in terms of
different downloader families, but also in techniques used to distribute,
secure and hide malicious downloads.
We summarized our paper as follows:
Downloaders are malicious programs with the goal to subversively
download and install malware (eggs) on a victim's machine. In this paper, we analyze
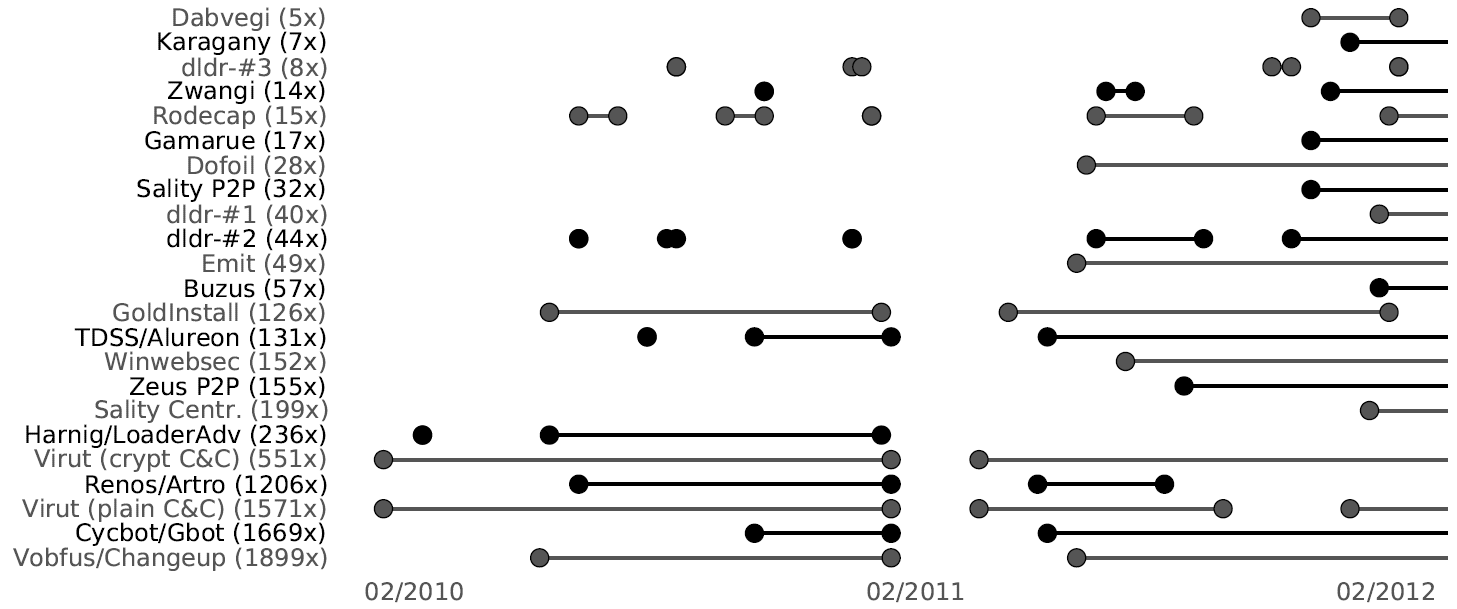
and characterize 23 Windows-based malware downloaders. We first show
a high diversity in downloaders' communication architectures (e.g., P2P), carrier
protocols and encryption schemes. Using dynamic malware analysis traces from
over two years, we observe that 11 of these downloaders actively operated for at
least one year, and identify 18 downloaders to be still active.
We then describe
how attackers choose resilient server infrastructures. For example, we reveal that
20% of the C&C servers remain operable on long term. Moreover, we observe
steady migrations between different domains and TLD registrars, and notice attackers
to deploy critical infrastructures redundantly across providers. After revealing
the complexity of possible counter-measures against downloaders, we
present two novel and generic techniques enabling defenders to actively acquire
malware samples.
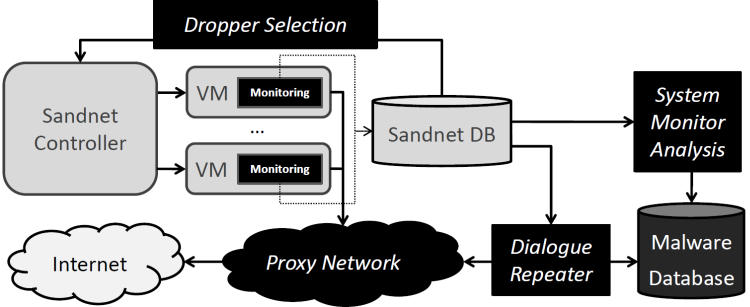
To do so, we leverage the publicly accessible downloader infrastructures
by replaying download dialogs or observing a downloader's process
activities from within the Windows kernel. With these two techniques, we successfully
milk and analyze a diverse set of eggs from downloaders with both plain
and encrypted communication channels.
I will present our work at DIMVA in Heraklion (Crete, Greece) on Thursday/Friday
July 26-27th 2012. I look forward to meeting you there! Please send me an email
if you are interested in an early copy of the paper.
Yours
Christian
|



